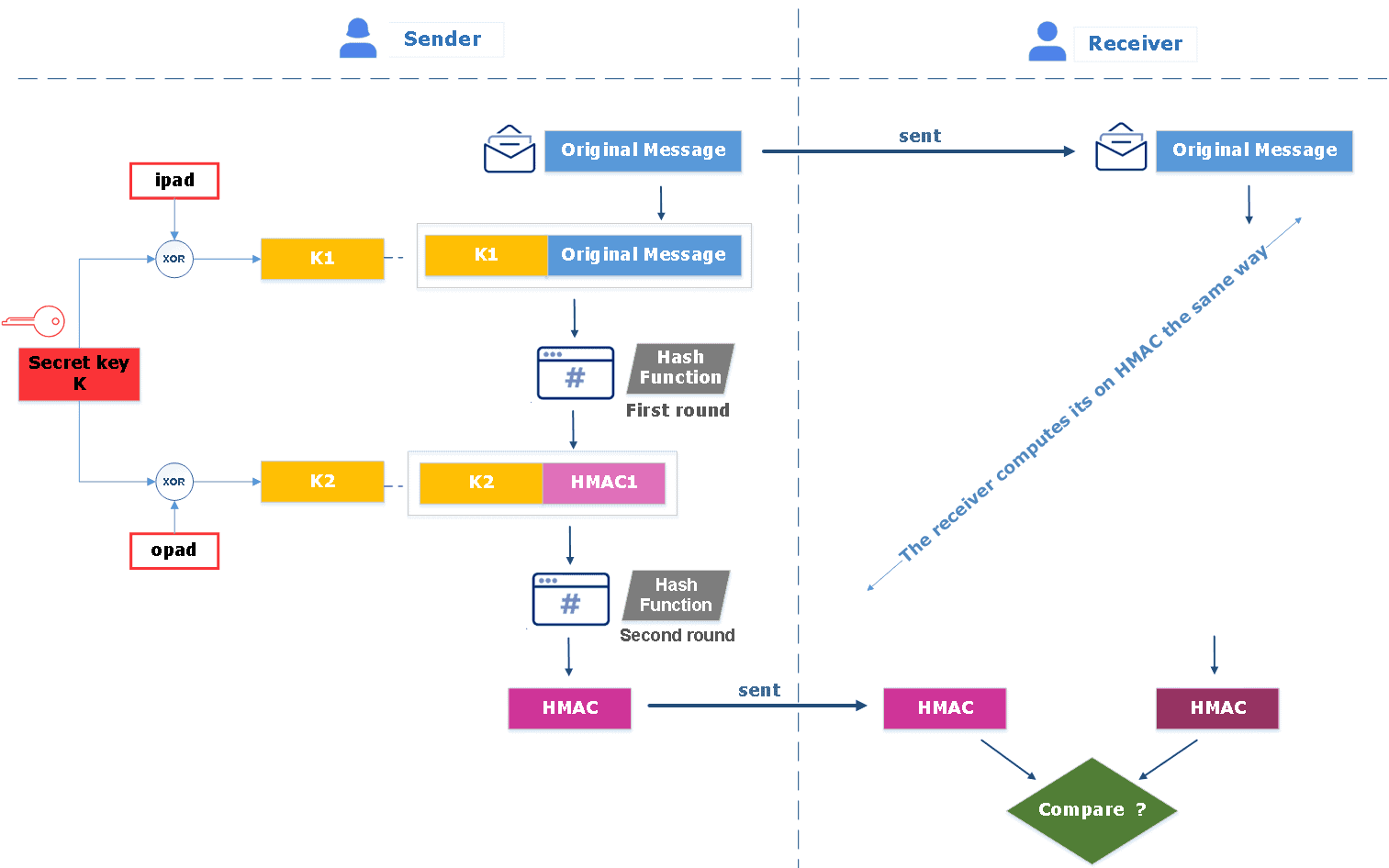
![Hash Techniques] : Message Authentication Code MAC, HMAC and Password Salting | Ammar Hasayen - Blog Hash Techniques] : Message Authentication Code MAC, HMAC and Password Salting | Ammar Hasayen - Blog](https://ammarhasayen.files.wordpress.com/2015/02/mac6.png)
Hash Techniques] : Message Authentication Code MAC, HMAC and Password Salting | Ammar Hasayen - Blog

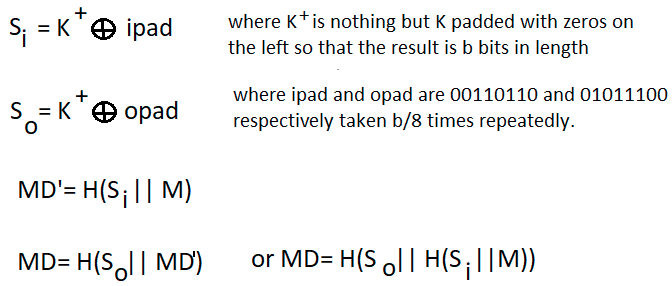
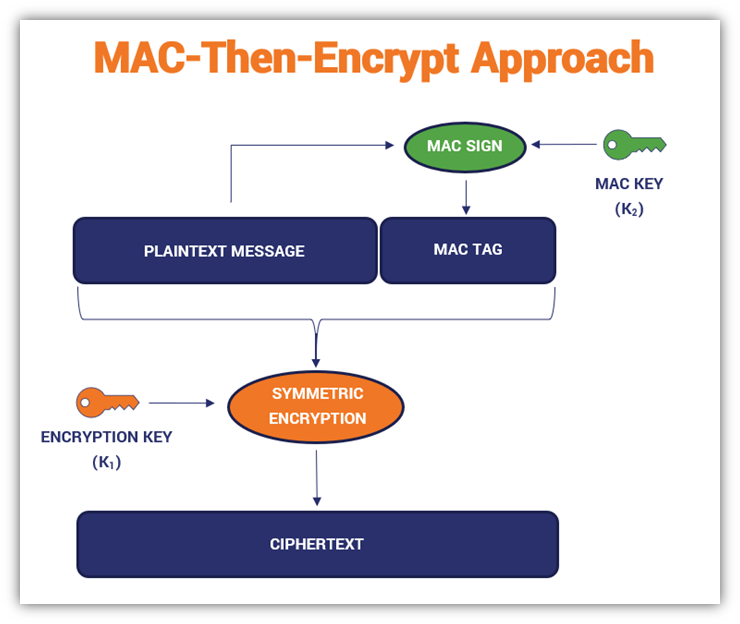
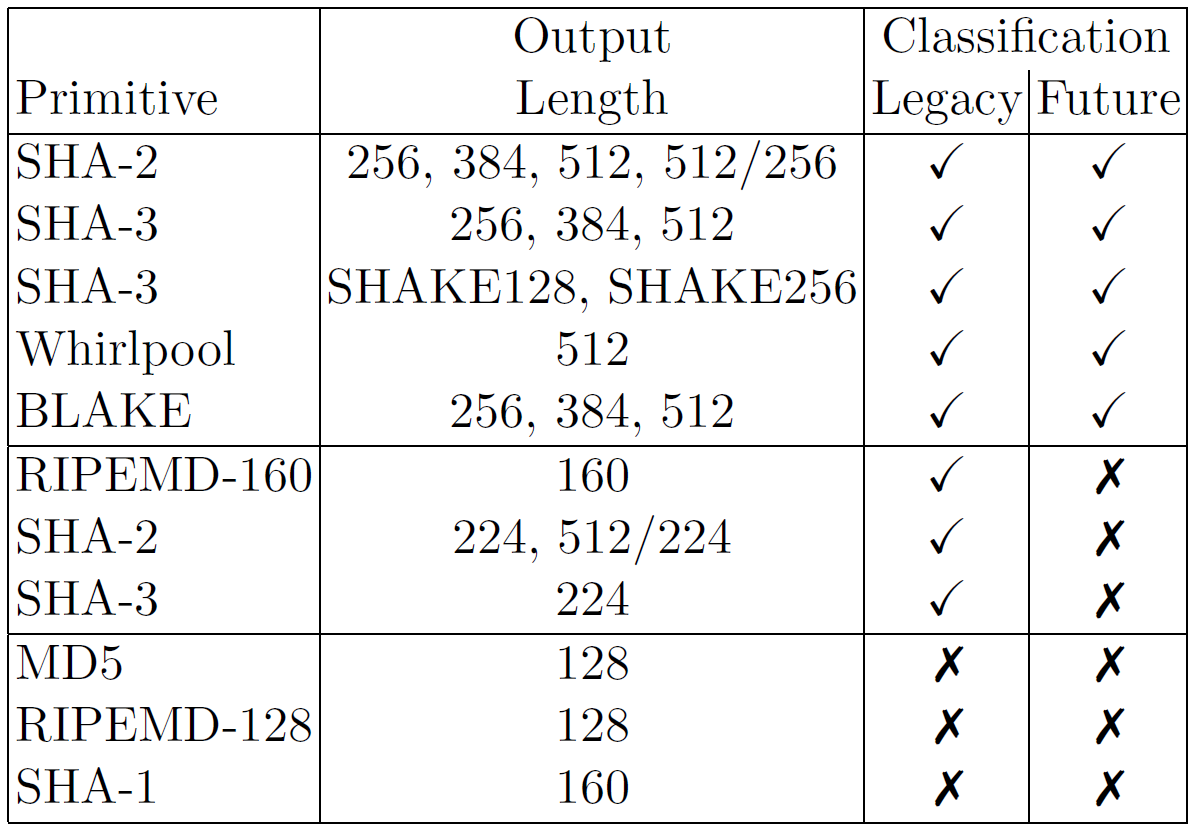
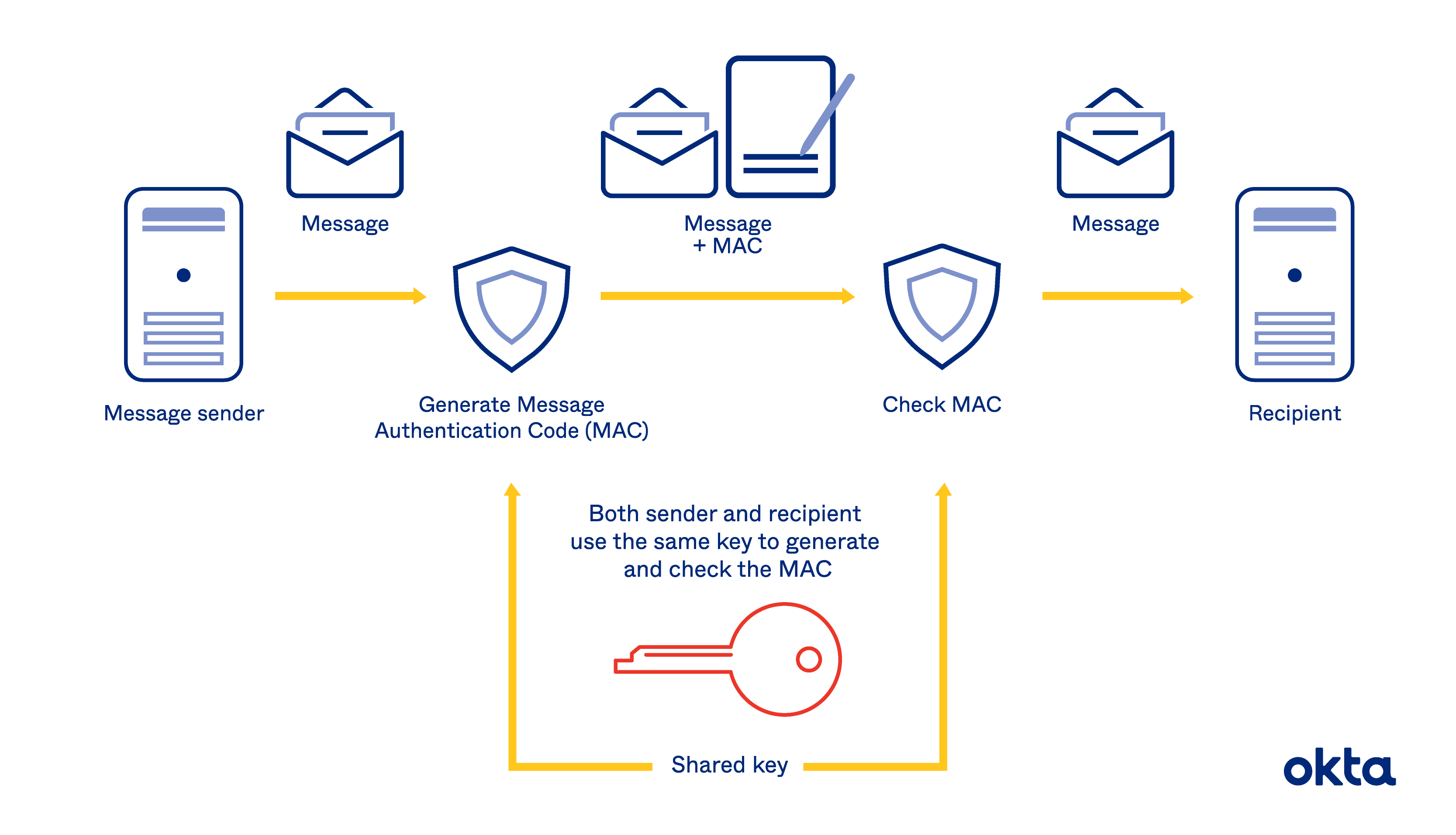
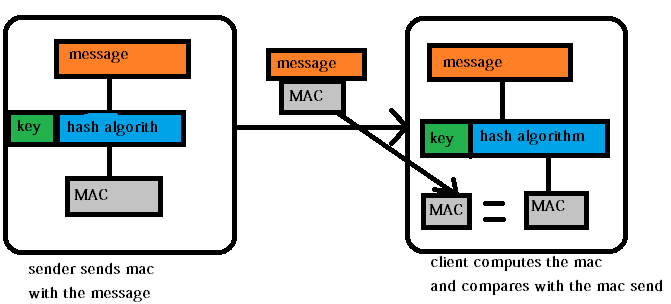
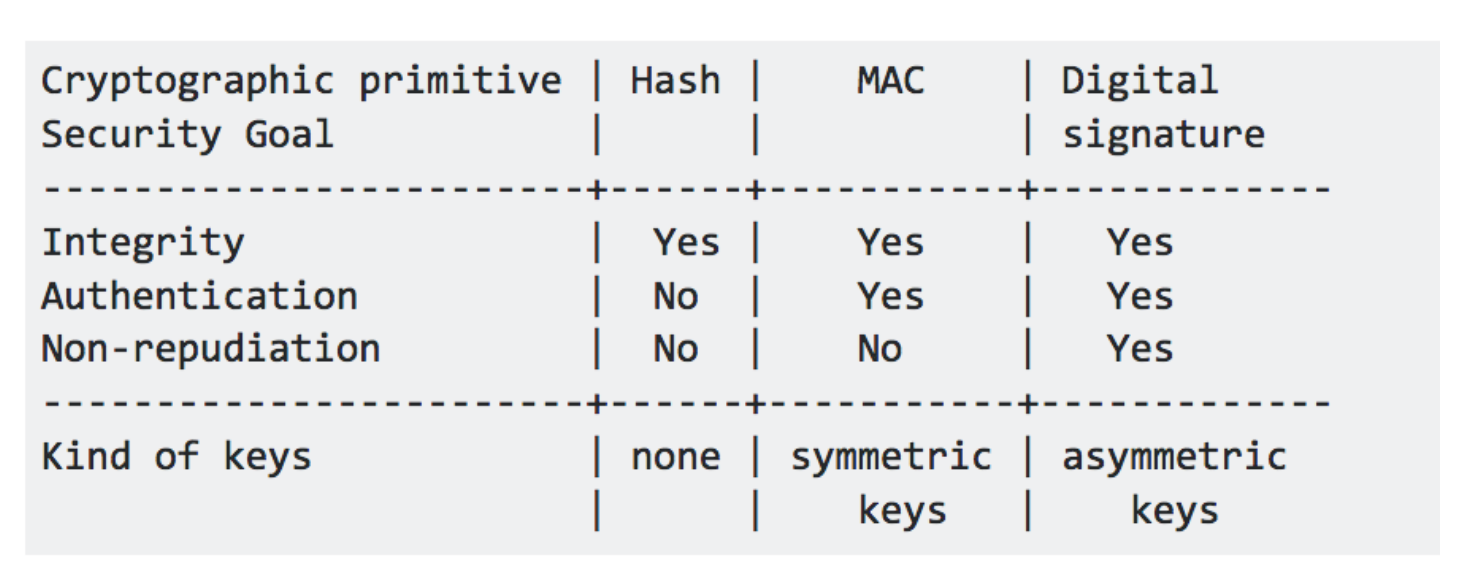
Difference-Between-MAC-and-HMAC-Comparison-Summary - MAC VERSUS HMAC MAC HMAC Short piece of information Specific type of MAC that used to | Course Hero

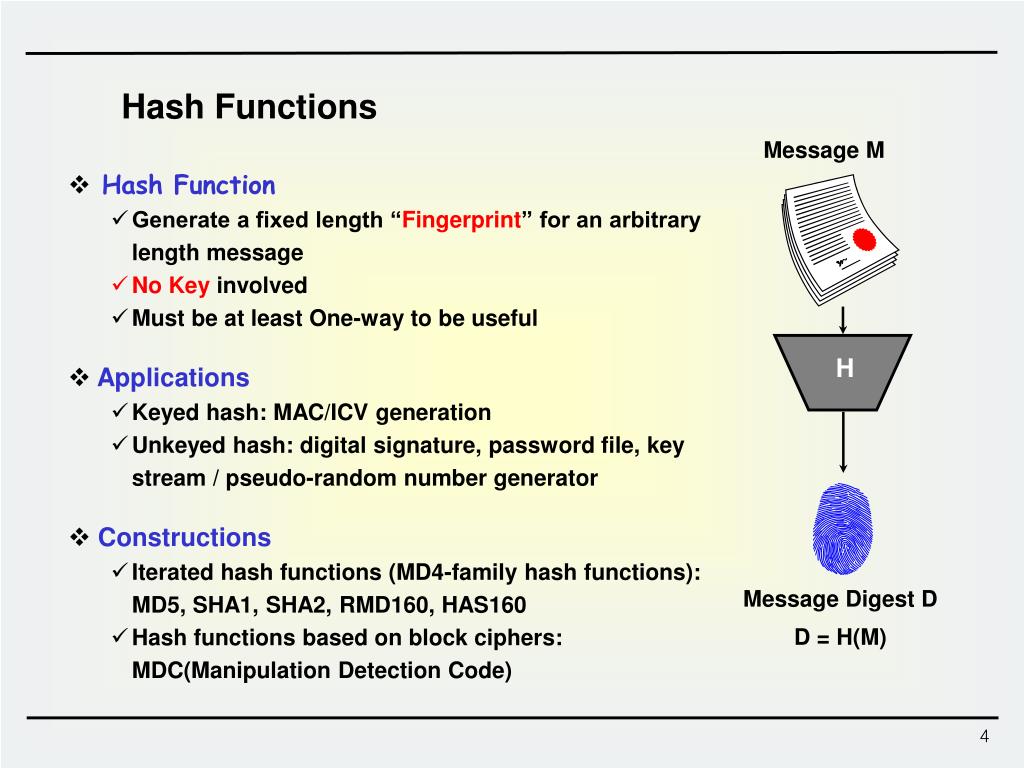
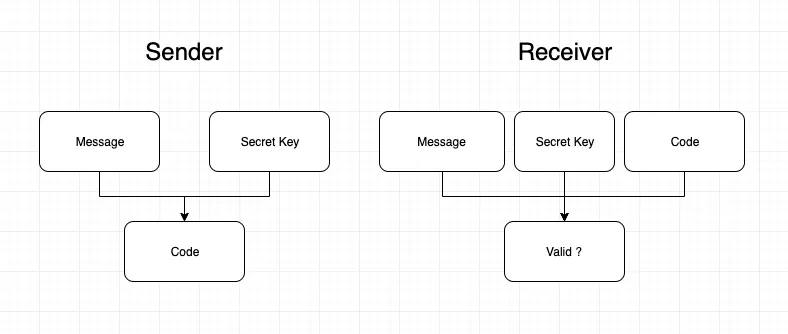
Lect : Hash Functions and MAC. 2 1.Introduction - Hash Function vs. MAC 2. Hash Functions Security Requirements Finding collisions – birthday. - ppt download