Sensors | Free Full-Text | A Dynamic Four-Step Data Security Model for Data in Cloud Computing Based on Cryptography and Steganography
Sensors | Free Full-Text | A Dynamic Four-Step Data Security Model for Data in Cloud Computing Based on Cryptography and Steganography


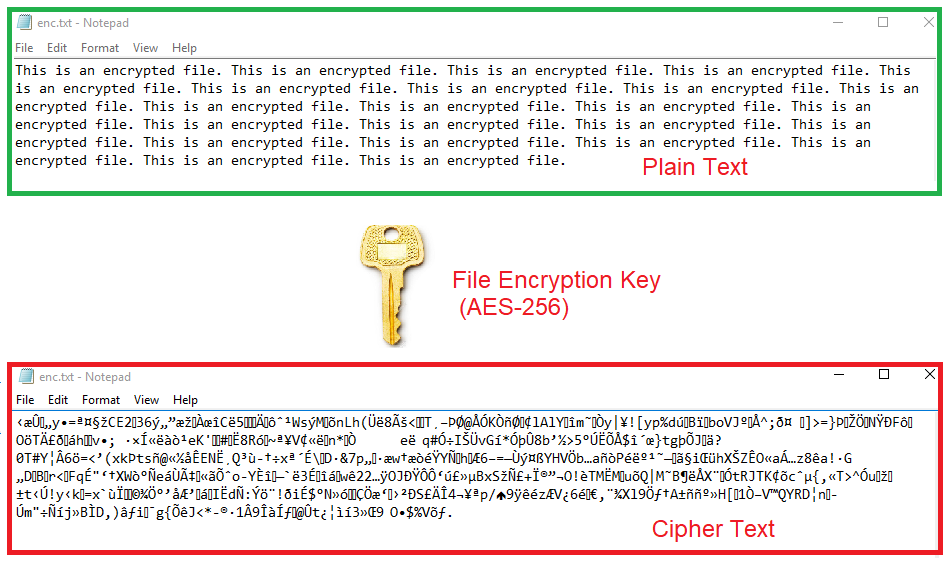
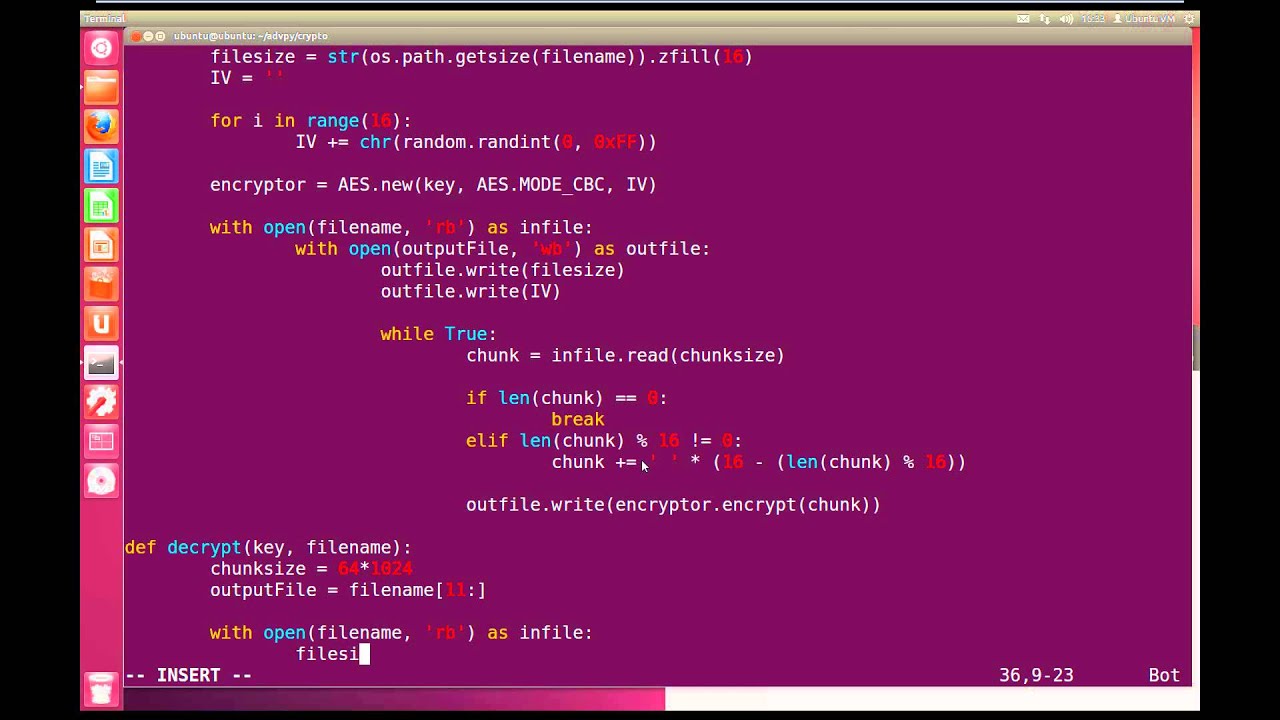
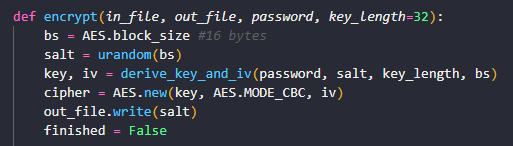
![Protect your TCP tunnel by implementing AES encryption with Python [Tutorial] | Packt Hub Protect your TCP tunnel by implementing AES encryption with Python [Tutorial] | Packt Hub](https://packt-type-cloud.s3.amazonaws.com/uploads/sites/2432/2018/05/3290de4e-cb61-473f-a975-4bf5559170e5.png)