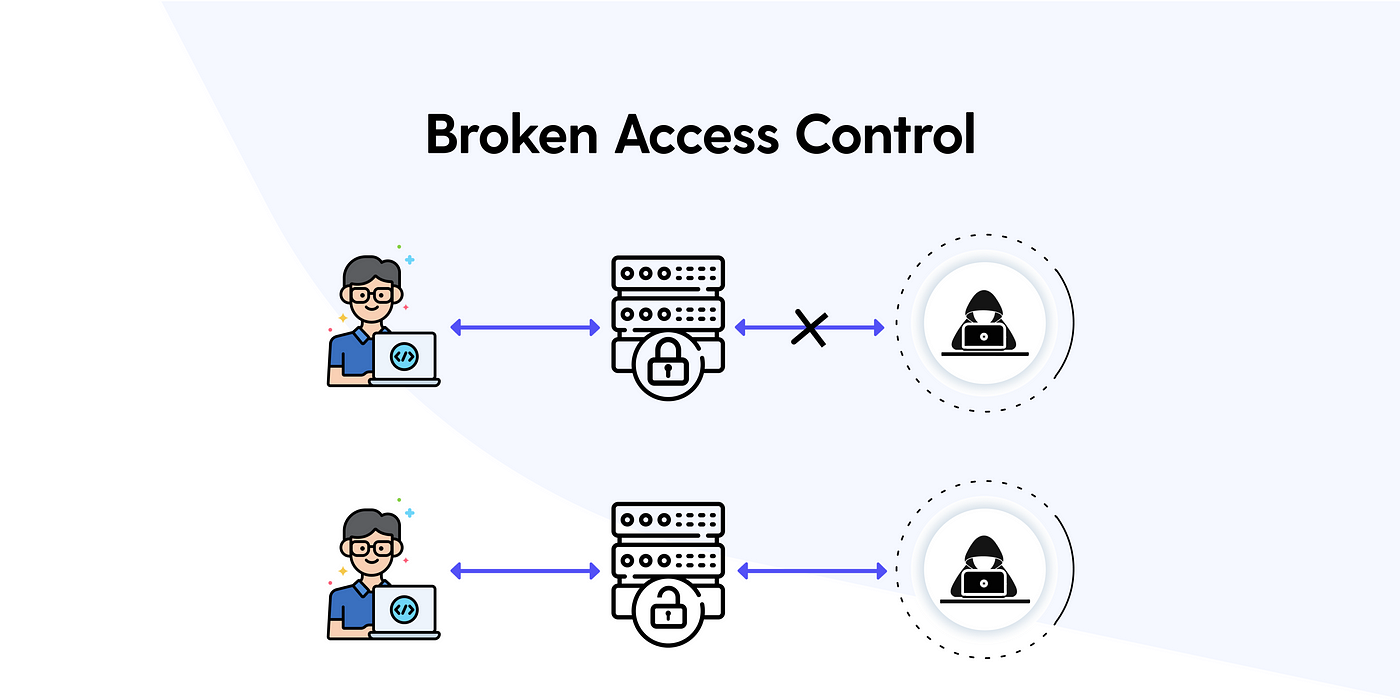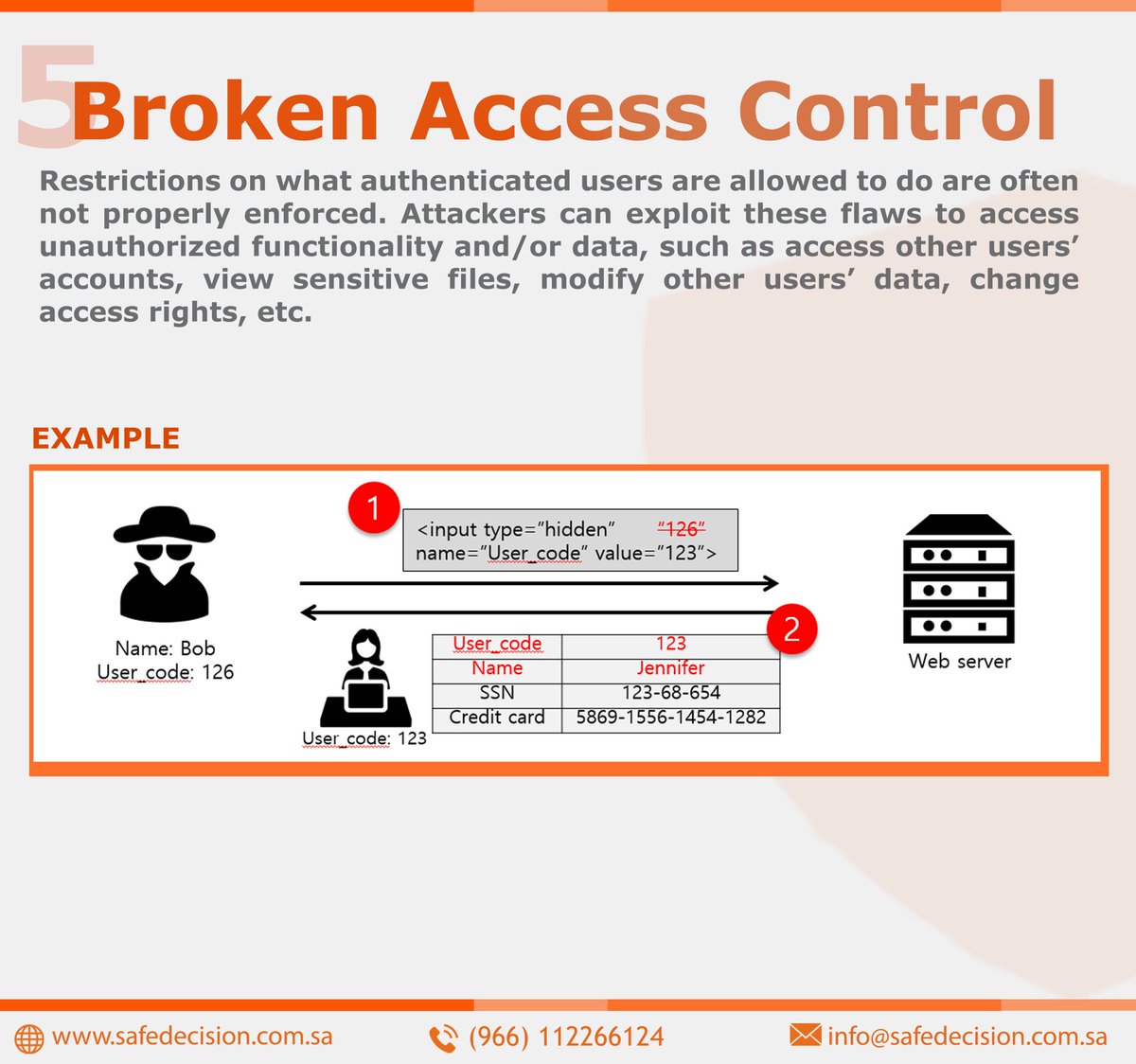
Safe Decision Co. on Twitter: "#Web Application Security Risks. 5-Broken Access Control: #CyberSecurity https://t.co/cYHfvcrKCD" / Twitter

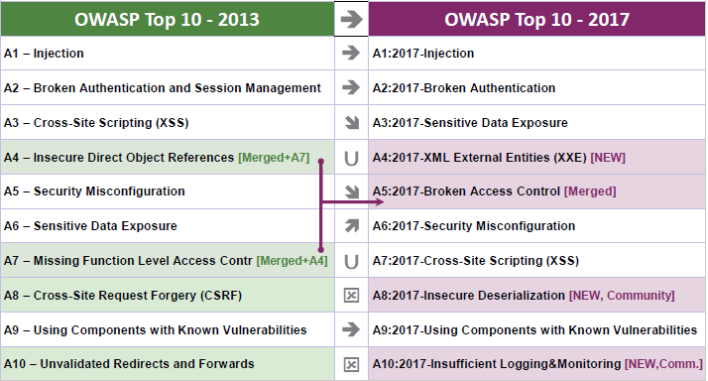
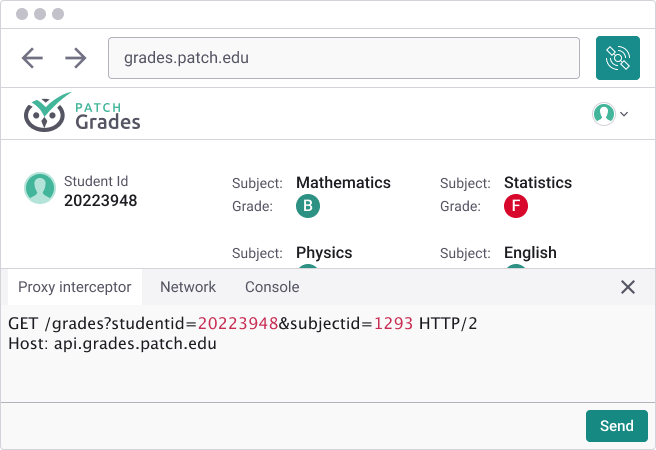
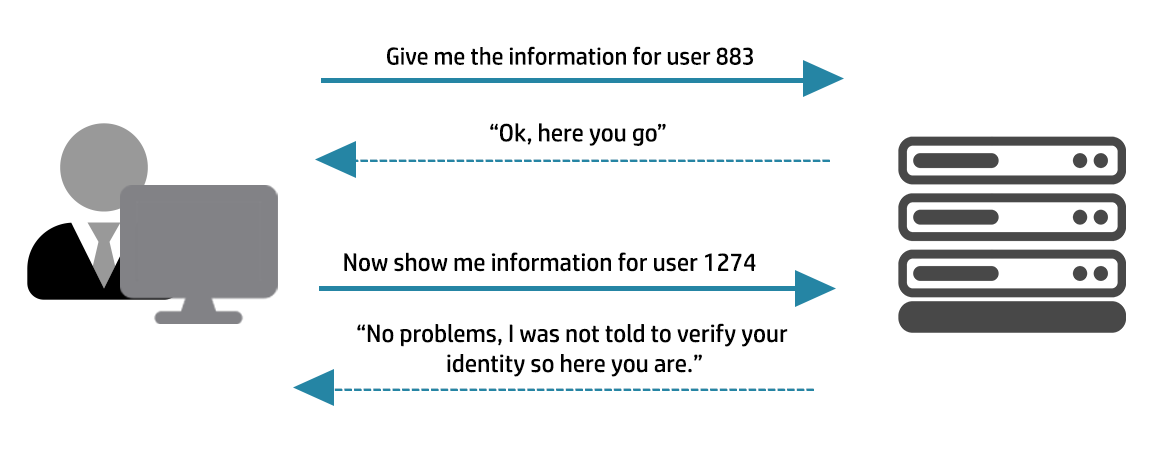
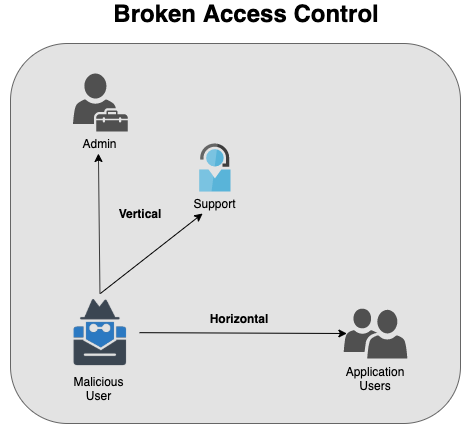
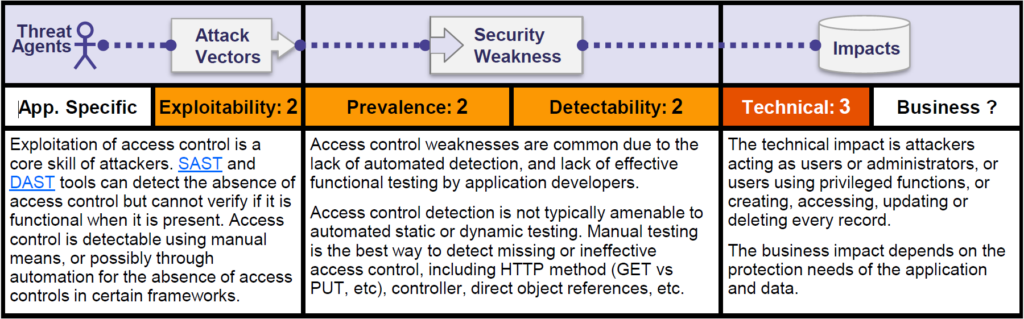
How to Catch the Top OWASP 2021 Security Category - Broken Access Control - in Code Review | PullRequest Blog

OWASP Top 10: #5 Broken Access Control and #6 Security Misconfiguration (2019) Online Class | LinkedIn Learning, formerly Lynda.com
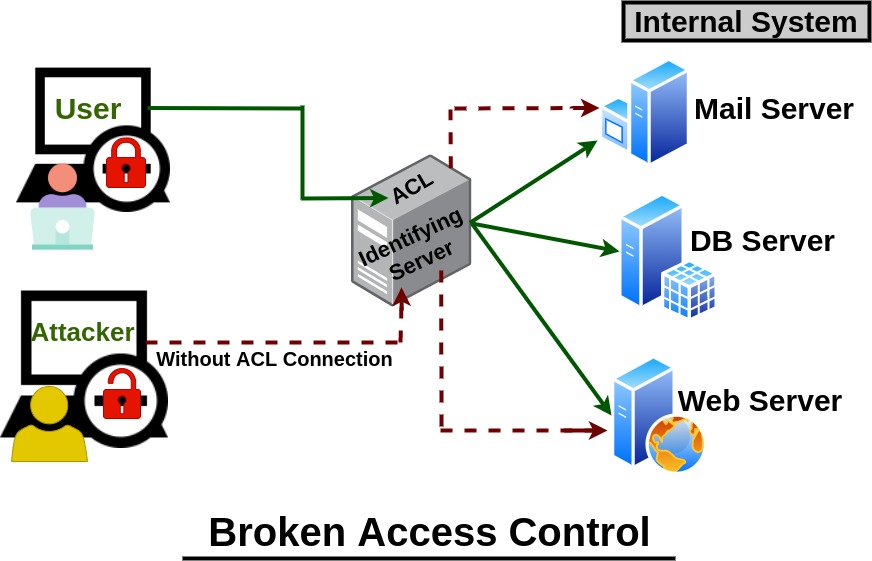
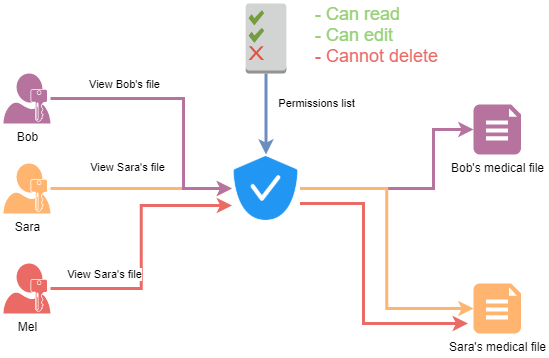
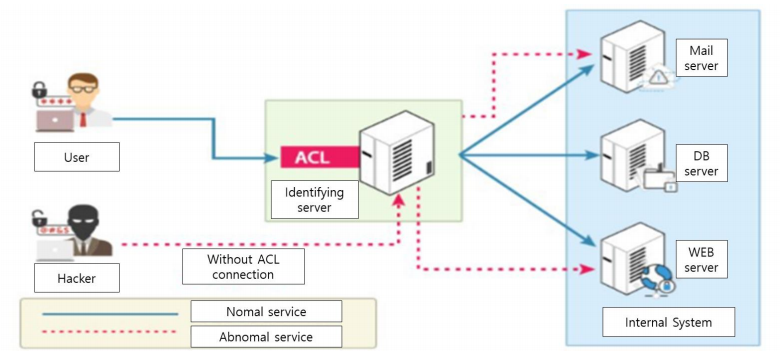
Comprehension The Risk of "Broken Authentication & Broken Access Control" - The most popular web application threats - Cloudkul