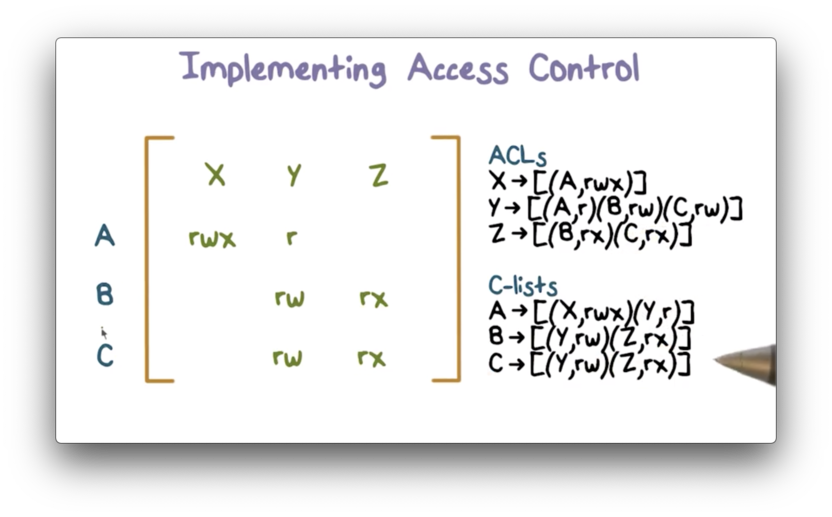
Semantic Technology Access Control Using DatasetsAI3:::Adaptive InformationAI3:::Adaptive Information

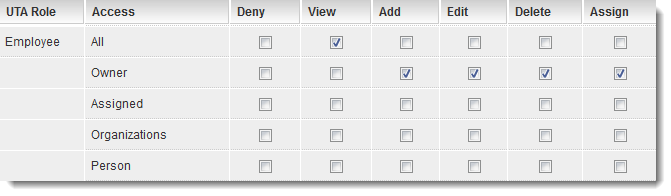
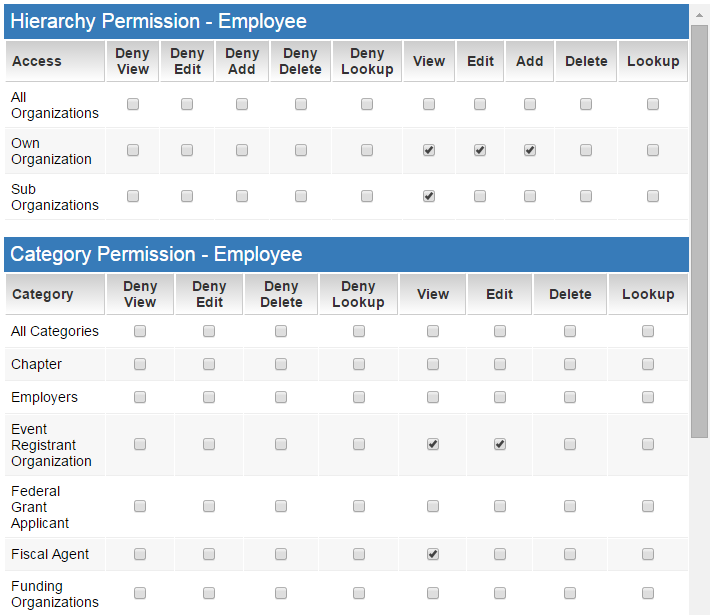
Understanding Access Control for Column Tags - Product Documentation - Treasure Data Product Documentation

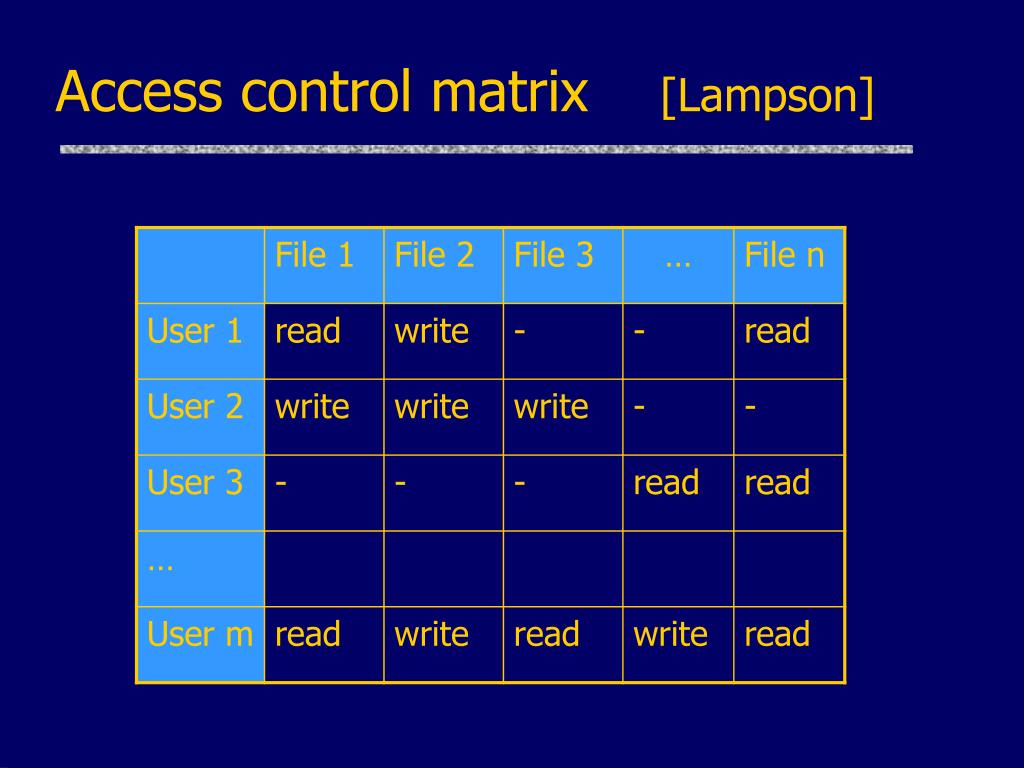
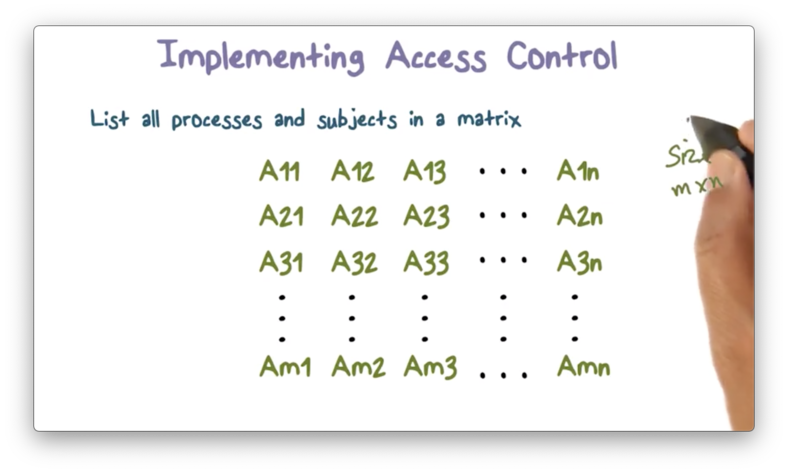
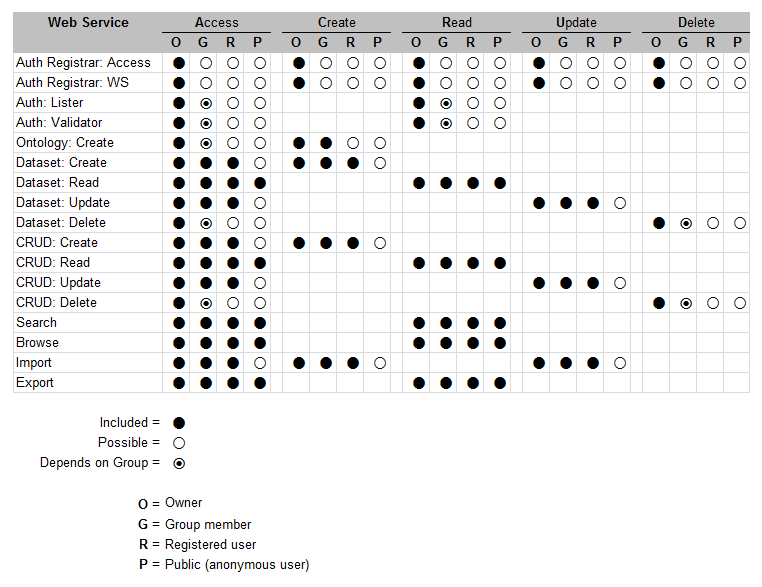
IP 2 DM access control matrix for each role: User, LAG DBA and Server... | Download Scientific Diagram